How Cybersecurity Threats Are Evolving in the USA
The digital landscape in the United States is shifting beneath our feet. As we become increasingly dependent on interconnected systems for everything from banking to national defense, the shadows lurking within those networks are growing darker and more complex. It wasn’t long ago that a cyber attack meant a simple virus disrupting a home computer or a defaced website. Today, the stakes are exponentially higher.
Our reliance on technology has created a massive attack surface. Every smartphone, smart thermostat, cloud server, and remote workstation is a potential entry point for malicious actors. This expansion isn’t just about volume; it’s about the sophisticated nature of the threats themselves. Hackers are no longer just lone wolves in hoodies; they are organized crime syndicates and state-sponsored groups equipped with cutting-edge tools.
Understanding the trajectory of these dangers is no longer just an IT problem—it is a critical necessity for business leaders, policymakers, and private citizens alike. To navigate this new era safely, we must first understand exactly how cybersecurity threats are evolving in the USA and what that means for our future.
What Are Cybersecurity Threats?
At its core, a cybersecurity threat is any malicious act that seeks to damage data, steal information, or disrupt digital life. These threats generally fall into broad categories: malware, phishing, denial of service (DoS), and man-in-the-middle attacks. However, the ecosystem of cybersecurity threats in the USA is far more nuanced than simple definitions suggest.
We must distinguish between cybercrime and cyber warfare. Cybercrime is typically financially motivated—think of credit card theft or ransomware designed to extort money from a hospital. Cyber warfare, on the other hand, involves politically motivated attacks often orchestrated by nation-states to destabilize infrastructure, steal intellectual property, or conduct espionage.
The targets are as varied as the methods. Individuals are targeted for their personal data and bank accounts. Businesses are hunted for trade secrets and customer databases. Perhaps most alarmingly, government entities and critical infrastructure—power grids, water treatment plants, and transportation networks—are increasingly in the crosshairs. The democratization of hacking tools means that powerful cyber weapons are now available to a wider range of criminals, blurring the lines between petty theft and national security crises.
How Cybersecurity Threats Are Evolving
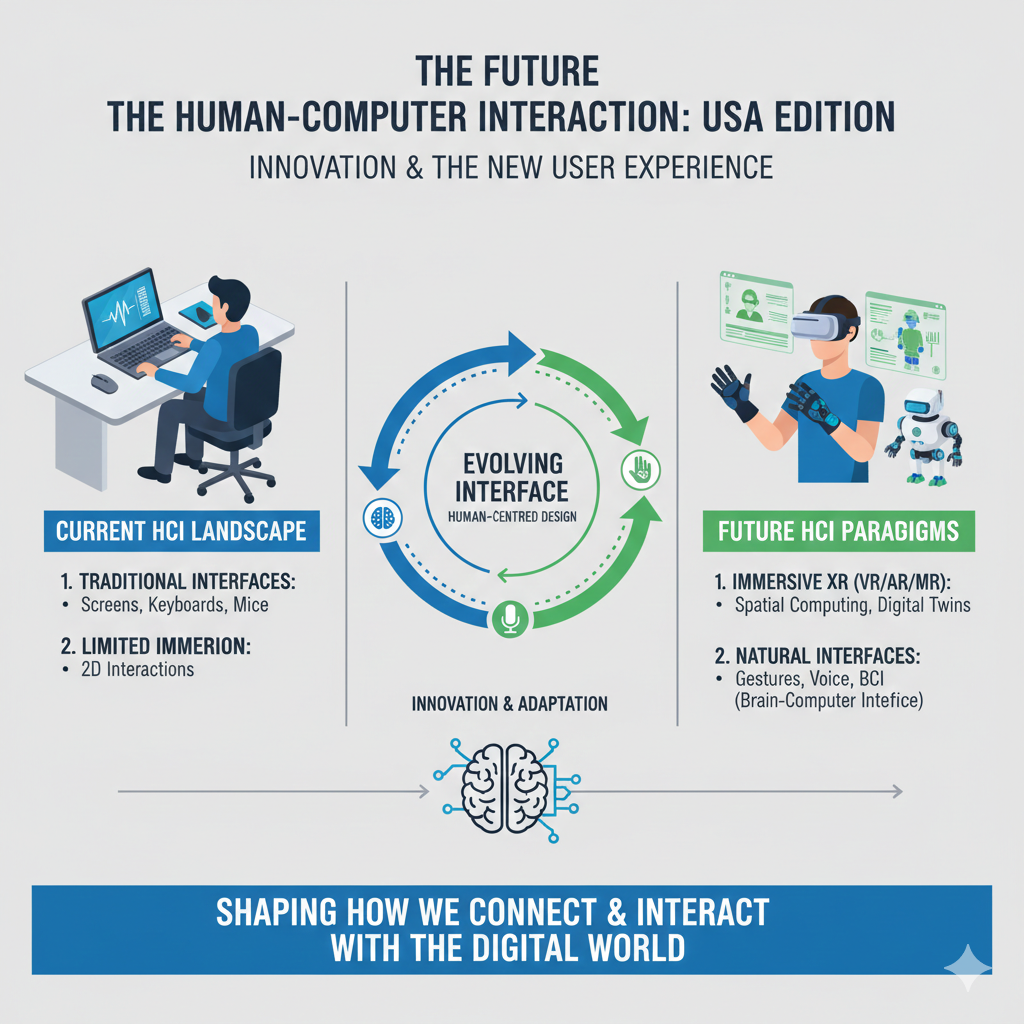
The speed at which the threat landscape changes is breathtaking. If we look at how cybersecurity threats are evolving in the USA, we see a clear trend toward increased sophistication and ruthlessness. The days of “spray and pray” attacks—where hackers sent out millions of spam emails hoping for a single hit—are fading. They are being replaced by highly targeted, strategic campaigns.
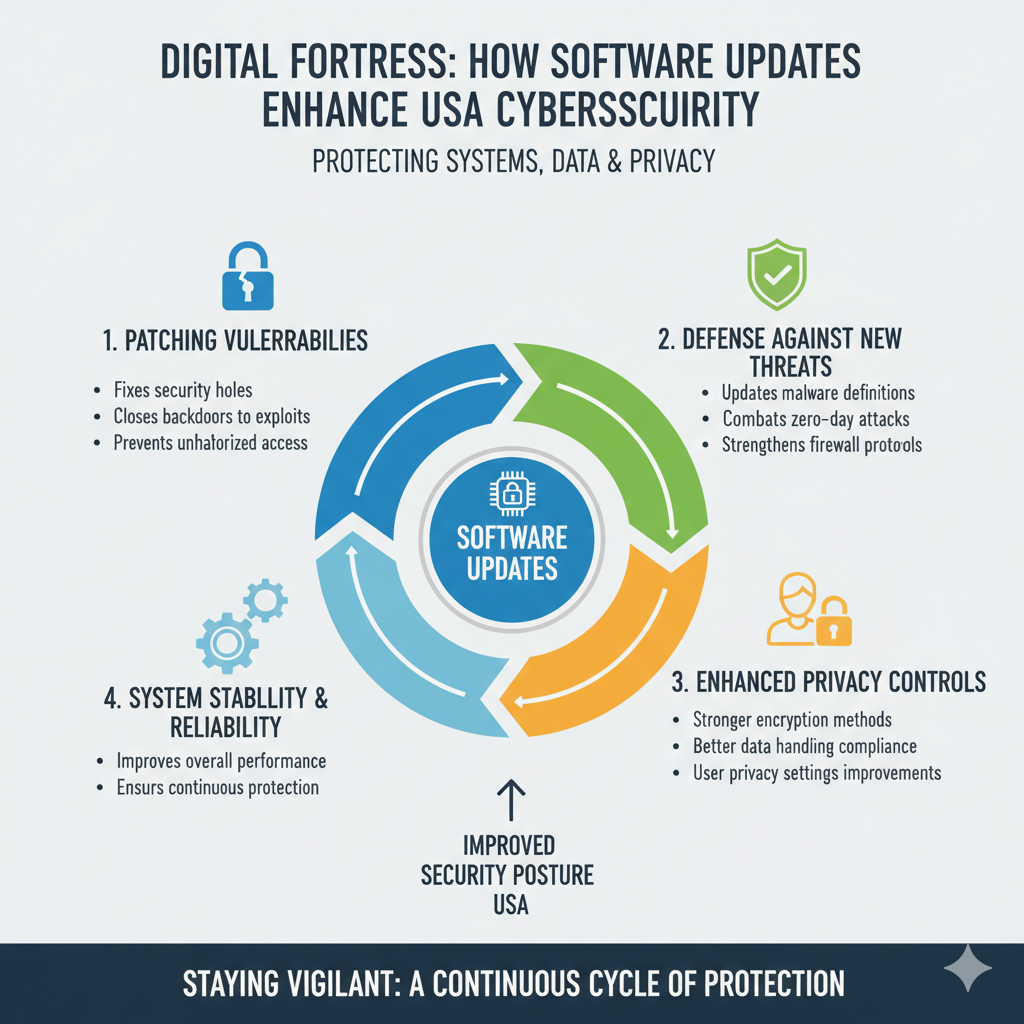
One of the most significant shifts is the speed of execution. In the past, there might have been a significant lag between a vulnerability being discovered and it being exploited. Now, that window has shrunk to days or even hours. Attackers are moving faster, weaponizing new vulnerabilities before patches can be developed or deployed.
Furthermore, the barrier to entry has lowered. “Cybercrime-as-a-Service” (CaaS) allows individuals with little technical knowledge to rent sophisticated hacking tools on the dark web. This commercialization of cyber threats means that the volume of attacks is increasing alongside their complexity, overwhelming traditional defense mechanisms.
Rise of Ransomware and Extortion Attacks
Ransomware has arguably become the most visible and destructive face of modern cybercrime. Ransomware attacks in the USA have evolved from simple encryption schemes into multi-layered extortion operations.
Initially, ransomware simply locked a victim’s files and demanded payment for the decryption key. While this remains a threat, savvy organizations began using robust backups to restore data without paying. In response, criminals adopted “double extortion” tactics. Now, they don’t just lock the data; they steal it first. If the victim refuses to pay the ransom for the key, the attackers threaten to leak sensitive data publicly. Some groups have even escalated to “triple extortion,” where they also threaten the victim’s customers or partners, maximizing the pressure to pay.
The targets have shifted, too. Attackers are ruthlessly targeting critical infrastructure and essential services where downtime is not an option. From the Colonial Pipeline disruption to attacks on healthcare systems during the pandemic, the strategy is clear: inflict maximum pain to ensure a quick payout. The financial and operational impact of these attacks costs the US economy billions of dollars annually, not to mention the reputational ruin left in their wake.
Phishing, Social Engineering & Identity Theft
While technology advances, the weakest link in cybersecurity remains the human element. Phishing attacks in the USA are becoming terrifyingly convincing, moving far beyond the obvious scams of the past.
Social engineering—the art of manipulating people into divulging confidential information—has been supercharged by technology. We are seeing a rise in “spear phishing” and “whaling,” where attackers meticulously research their targets (often high-level executives) to craft personalized messages that are nearly indistinguishable from legitimate communications.
The rise of generative AI has added fuel to this fire. Attackers can now use AI to generate flawless emails in any language, removing the grammatical errors that used to be tell-tale signs of a scam. Deepfake technology is also entering the fray, with criminals using voice cloning to impersonate CEOs or family members to authorize money transfers. These advanced credential harvesting techniques make it increasingly difficult for employees and individuals to trust their own inboxes.
AI and Automation in Cyber Attacks
The same artificial intelligence that promises to revolutionize medicine and transportation is also being weaponized by adversaries. AI cybersecurity threats represent a new frontier in the digital arms race.
Attackers are using machine learning to automate the process of scanning for vulnerabilities. Instead of manually searching for a weak point in a company’s firewall, an AI script can scan thousands of ports and systems in seconds, identifying soft targets with ruthless efficiency.
Moreover, we are seeing the emergence of adaptive malware. These are malicious programs that can use AI to change their behavior to avoid detection by security software. If a security protocol blocks one method of entry, the AI can rewrite the code in real-time to try a different approach. This creates a scenario of “AI vs. AI,” where defensive algorithms must battle offensive algorithms at speeds no human analyst can match.
Cloud, Remote Work & IoT Security Risks
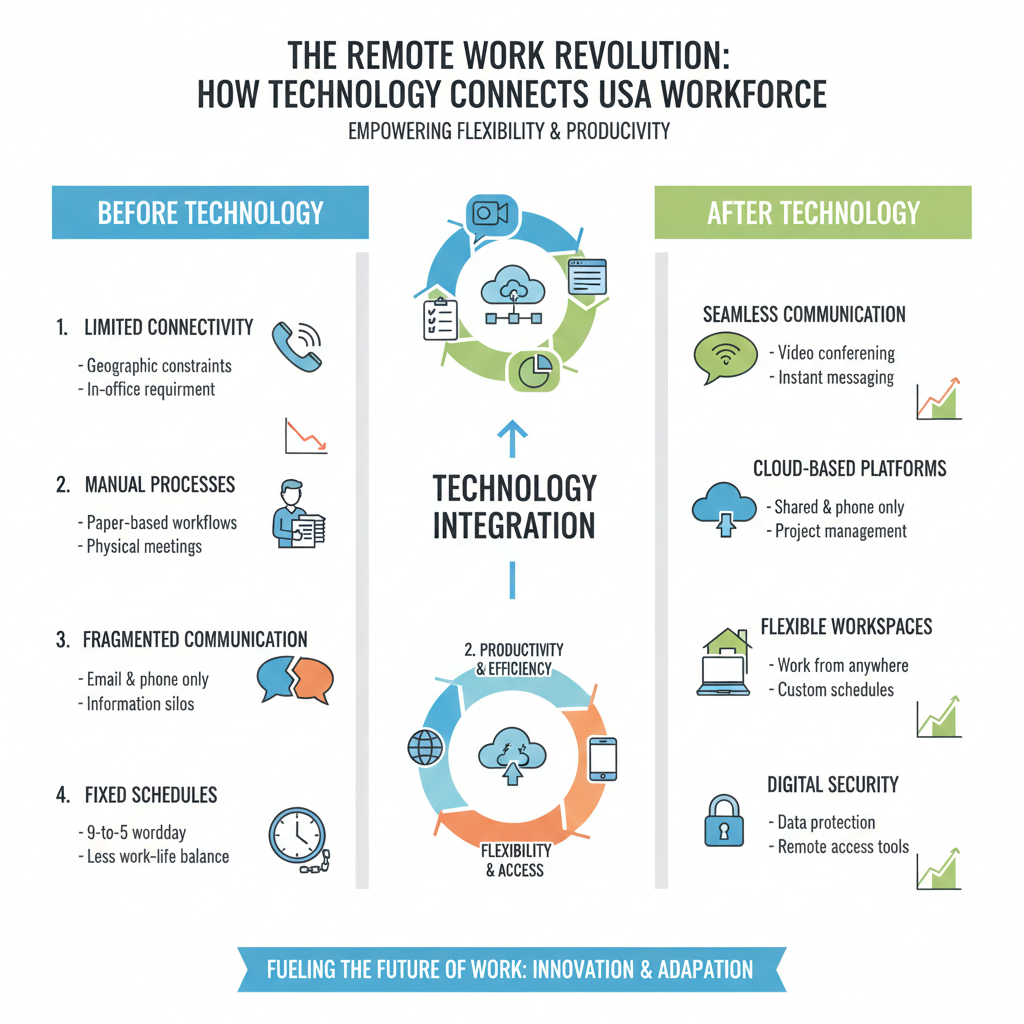
The way we work has changed fundamentally, and with that change comes new risk. As organizations migrate data off-premise, cloud security threats in the USA have skyrocketed. While major cloud providers generally offer robust security, the issue often lies in configuration. Misconfigured cloud environments—where a user accidentally leaves a storage bucket public instead of private—are a leading cause of massive data breaches.
The permanent shift to remote and hybrid work models has further dissolved the traditional security perimeter. Employees accessing corporate networks from personal devices or unsecured coffee shop Wi-Fi networks create thousands of potential entry points that IT teams struggle to monitor.
Simultaneously, the explosion of the Internet of Things (IoT) has introduced billions of insecure devices into our networks. From smart fridges in breakrooms to connected sensors on factory floors, these devices often lack basic security features like strong passwords or update capabilities. Hackers can hijack these devices to form botnets or use them as stepping stones to access more critical systems within a network.
Supply Chain & Third-Party Cyber Risks
One of the most insidious trends in recent years is the shift toward indirect attacks. Instead of attacking a well-defended fortress directly, hackers are poisoning the water supply. Supply chain cyber attacks in the USA focus on compromising the smaller, less secure vendors that service larger organizations.
The SolarWinds hack is the prime example of this. By compromising a widely used software update, attackers gained access to thousands of government and corporate networks simultaneously. These vendor-based breaches are particularly dangerous because they exploit the trust relationships between businesses.
Software dependency risks are also a major concern. Modern applications are built using libraries of third-party code. If a vulnerability is found in a widely used open-source library (like the Log4j incident), it can leave millions of applications vulnerable overnight. Verifying the security of every third-party vendor and software component is a monumental challenge, yet it is essential for modern security.
Impact of Evolving Cyber Threats
The consequences of failing to adapt to this changing landscape are severe. The cyber threat impact in the USA is measured not just in dollars, but in trust and stability.
Financially, the costs are staggering. Beyond the immediate ransom payments or theft of funds, companies face costs for forensic investigation, legal fees, regulatory fines, and system restoration. For small businesses, a single significant breach can be an extinction-level event.
Data privacy violations leave millions of Americans vulnerable to identity theft and fraud, eroding the public’s sense of safety online. Perhaps most damaging is the long-term blow to reputation and trust. Customers are increasingly hesitant to do business with companies that cannot protect their data. In an economy driven by information, trust is a currency that, once lost, is incredibly difficult to earn back.
How Organizations Are Responding
In the face of these escalating threats, complacency is not an option. Cybersecurity strategies in the USA are shifting from reactive to proactive stances.
The most significant strategic shift is the adoption of “Zero Trust” security models. The old motto was “trust but verify.” The new reality is “never trust, always verify.” In a Zero Trust architecture, no user or device is trusted by default, even if they are already inside the network perimeter. Verification is required for every request to access resources.
Organizations are also investing heavily in advanced threat detection. This includes Extended Detection and Response (XDR) systems that collect data across email, endpoints, servers, and cloud workloads to provide a unified view of attacks.
Finally, there is a renewed focus on the human firewall. Cybersecurity training and awareness programs are moving beyond annual compliance videos. Companies are running simulated phishing campaigns and regular training sessions to ensure that employees—the first line of defense—remain vigilant against social engineering tactics.
Frequently Asked Questions (FAQ)
Q1. How are cybersecurity threats evolving in the USA?
Threats are becoming more automated, targeted, and sophisticated. Attackers are leveraging AI, exploiting supply chains, and using advanced social engineering to bypass traditional defenses.
Q2. Why are ransomware attacks increasing?
Ransomware is highly profitable and relatively low-risk for attackers, especially with the rise of cryptocurrencies that make tracing payments difficult. The “Ransomware-as-a-Service” model also allows non-technical criminals to launch attacks easily.
Q3. How does AI change cyber threats?
AI allows attackers to automate vulnerability scanning, generate convincing phishing emails, and create adaptive malware that can evade detection. It increases both the speed and scale of attacks.
Q4. What industries are most targeted by cyber attacks?
Healthcare, finance, energy, and government sectors are top targets due to the high value of their data and the critical nature of their operations (which makes them more likely to pay ransoms).
Q5. How can individuals protect themselves from cyber threats?
Use strong, unique passwords (managed by a password manager), enable Multi-Factor Authentication (MFA) on all accounts, keep software updated, and learn to recognize the signs of phishing emails.
Q6. Are cloud systems more vulnerable to attacks?
Not necessarily inherently, but they are vulnerable to misconfiguration. Human error in setting up cloud security permissions is a major cause of data breaches.
Q7. What does the future of cybersecurity look like?
The future will likely see an “arms race” between AI-driven attacks and AI-driven defense. We can also expect stricter government regulations and a universal shift toward Zero Trust architectures.
Final Thoughts: Staying Ahead of Evolving Cyber Threats
The evolution of cybersecurity threats in the USA paints a picture of a digital battleground that is constantly shifting. From the rise of AI-driven malware to the complex webs of supply chain vulnerabilities, the challenges are immense. However, they are not insurmountable.
The key takeaway for every American organization and individual is that security is not a product you buy; it is a process you practice. We must move away from the idea that we can be “100% secure” and instead focus on cyber resilience—the ability to anticipate, withstand, recover from, and adapt to adverse conditions. By staying informed, adopting proactive strategies like Zero Trust, and fostering a culture of security awareness, we can navigate this evolving landscape and protect our digital future.